Written by:
Guido Ronchetti, CTO at XTN Cognitive Security ®
Leaving behind 2022, it’s time to summarize what’s happened from a mobile malware evolution perspective. More than two years after the pandemic breakthrough, the digital services landscape has changed drastically, accelerating the adoption of complete digital services and quickly reducing the direct interactions between banks and end-users.
Those changes have also impacted the malware ecosystem. With the broader adoption of Strong Customer Authentication (SCA) features and the tighter controls of official app stores, malware developers had to find new ways to implement their fraudulent behavior. We are focusing the analysis on mobile malware because the trends and developments in this area have been more active compared to the web malware world, where there is a lack of significant evolution. Moreover, the main focus is on the Android operating system, as there are no reported cases of financial mobile malware that currently attack the iOS platform.
BANKING MALWARE EVOLUTION 2020-2022
XTN Cognitive Security®, as a security vendor, continuously monitors and evaluates the dynamics and trends we observe. Through our AI-driven malware analysis engine, we have watched the evolution of malware families over the years and recorded their various features. The following graph depicts the trend over the last three years, highlighting the progression of banking malware families from a numerical viewpoint between 2020 to 2022. This information is crucial in understanding the threat landscape and developing effective measures to protect against these malicious actors.
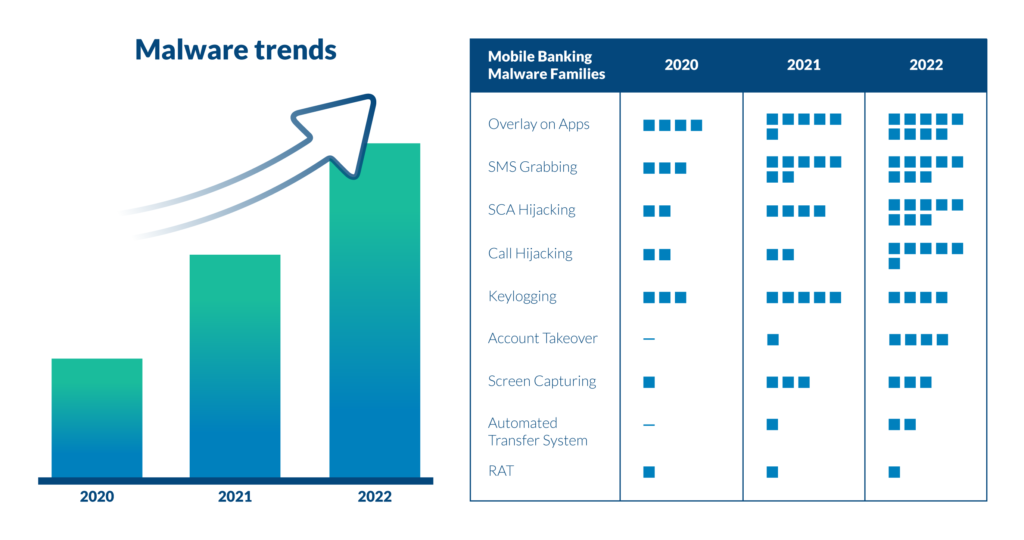
The XTN team has noticed a significant increase in the presence of Overlay on Apps, SMS Grabbing, Calls, and SCA Hijacking capabilities in the last two years. These features have dominated the malware landscape, becoming prevalent in the threat actors’ toolkits. It’s worth noting that other features, such as RAT and Keylogging, have remained stable over the last three years, maintaining a presence without significant growth in popularity. This information highlights the need for constant monitoring and adaptation to the evolving threat landscape in order to effectively protect against these malicious activities.
A NEW MALWARE ERA
We are currently in a new era of malware evolution. This era could be referred to as the Accessibility and Overlay era, as this is a common tactic adopted by most malware that emerged in 2018. Since then, numerous malware families with similar tactics have emerged, but what do they all have in common?
Common points:
- use accessibility services to access the relevant Android features;
- overlay target apps to gain the victim’s trust;
- intercept SMS and push notifications to hijack one-time passwords;
- harvest the victim’s data via keylogging and microphone interception, etc.
In late 2021 a new evolutionary trend started responding to some of the mitigations introduced to slow down the Accessibility and Overlay wave. The malware had two main obstacles to overcome:
- a higher sophistication of Strong Customer Authentication (SCA) technologies and moving from SMS to app-based tokens this only applies to Europe, following the adoption of the directives related to PSD2);
- increased diligence in store scrutiny before publishing apps.
Starting from the goal of controlling the SCA flow, this pushed malware to adopt new techniques, expressly:
- controlling the victim’s activities via screen capturing* of the device;
- introducing Automated Transfer Systems (ATS)**. ATS is one of the most advanced and powerful features in today’s malware, giving the fraudster the ability to orchestrate the fraud directly from the victim’s device with little or no interaction;
- call hijacking or manipulation to block the victim from calling for help or trick into trusting the fraudster’s calls.
The usual attack pattern relying on those features consists in:
- a victim is tricked into installing a malware app;
- malware harvests the phone number and sends it to the fraudster;
- the fraudster calls the victim impersonating the service provider;
- fraudster guides the victim in accessing the target app;
- fraudster blocks the victim’s interactions and takes control of the device interacting with the app (via one of the techniques mentioned);
- the victim is asked to authenticate the relevant transaction taking temporary control of the app;
- fraud is completed, and the device is reset to slow down a quick reaction from the victim.
The other evolutionary driver of bypassing the store’s scrutiny in the app submission process introduces new distribution patterns:
- droppers are used to distribute malware apps from official stores. The dropper is just a trojan horse that can install the actual malware. This way, the fraudster can bypass the store’s scrutiny by postponing the installation of the final malevolent code;
- using legitimate remote control apps that are publically available in the official stores, the fraudster can take advantage of the trustability of those apps;
- they focus the malware’s requirements on limited targets. For example, SMS Grabbing targeting services that still rely on SMS OTPs to work.
HOW WE SPOT MALWARE IN DIGITAL SERVICES
Malware operates and interacts with victims through technological attack patterns and increasingly by simulating human behavior. It is precisely through a holistic analysis of the phenomenon that XTN Cognitive Security can identify and block these attempts.
The XTN Cognitive Security Platform® uses behavioral analysis to detect malware. It categorizes new threats by recognizing similarities with known malware families, allowing for real-time response to potential risks.
Our focus is on common financially-focused attacks such as web injections, RAT, MiTB, MiTA, overlay attacks, SMS grabbing, and memory injections. Our precise evaluation allows clients to implement countermeasures and protect end-users without affecting their experience.
TRUST YOUR DIGITAL USER! Contact us for a demo. Fill out the form below.
* Screen capturing is a technology that lets you stream, cast or control the screen of a device.
** ATS allows malware to programmatically use the information stolen from the victim to initiate fraudulent transactions in an automated way, making the whole infection and fraud chain more flexible and scalable